
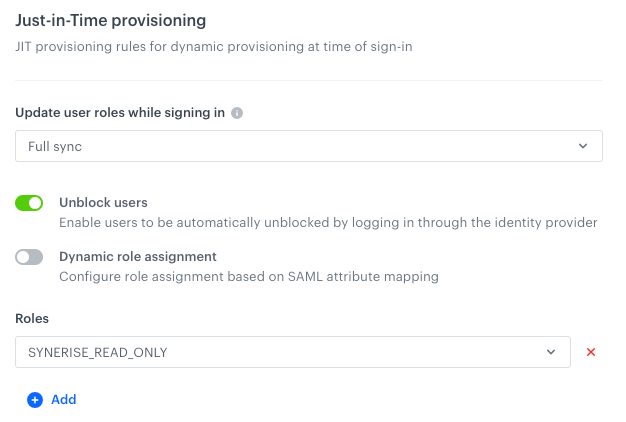
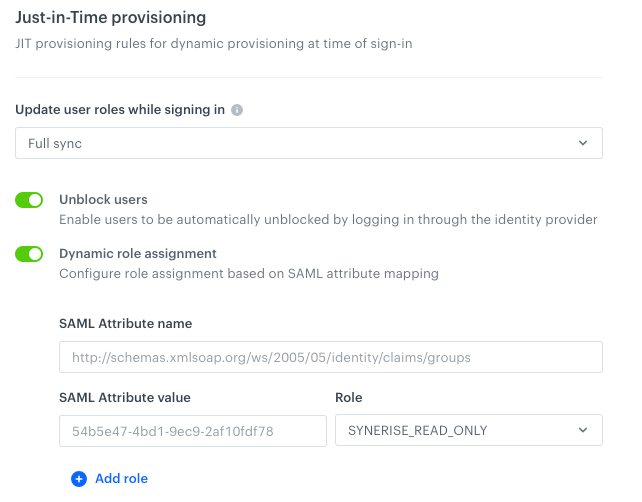
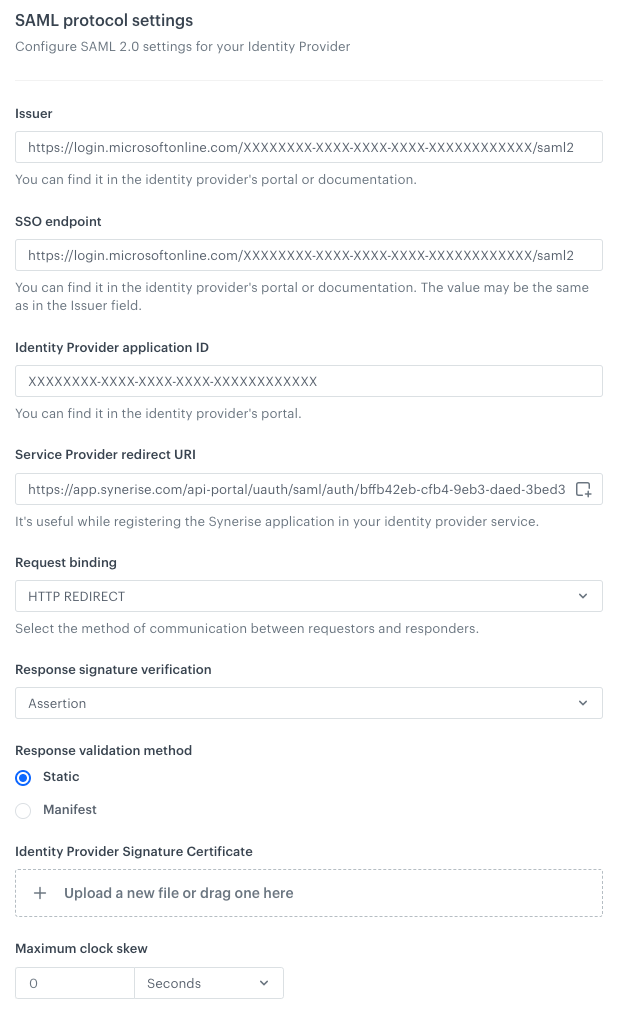
In the Synerise application, review the SAML setup for any typos or errors in the Just-In-Time provisioning configuration.
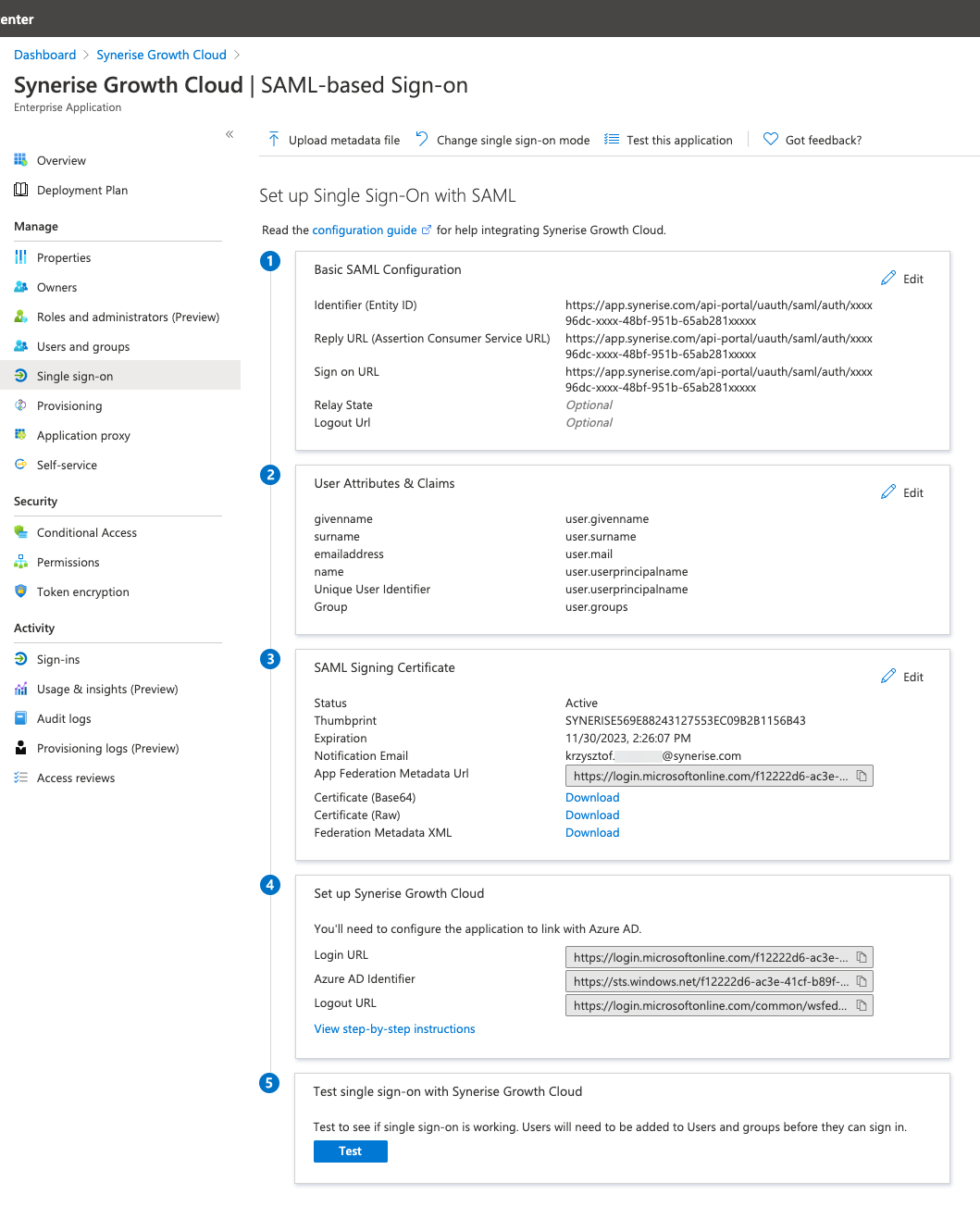
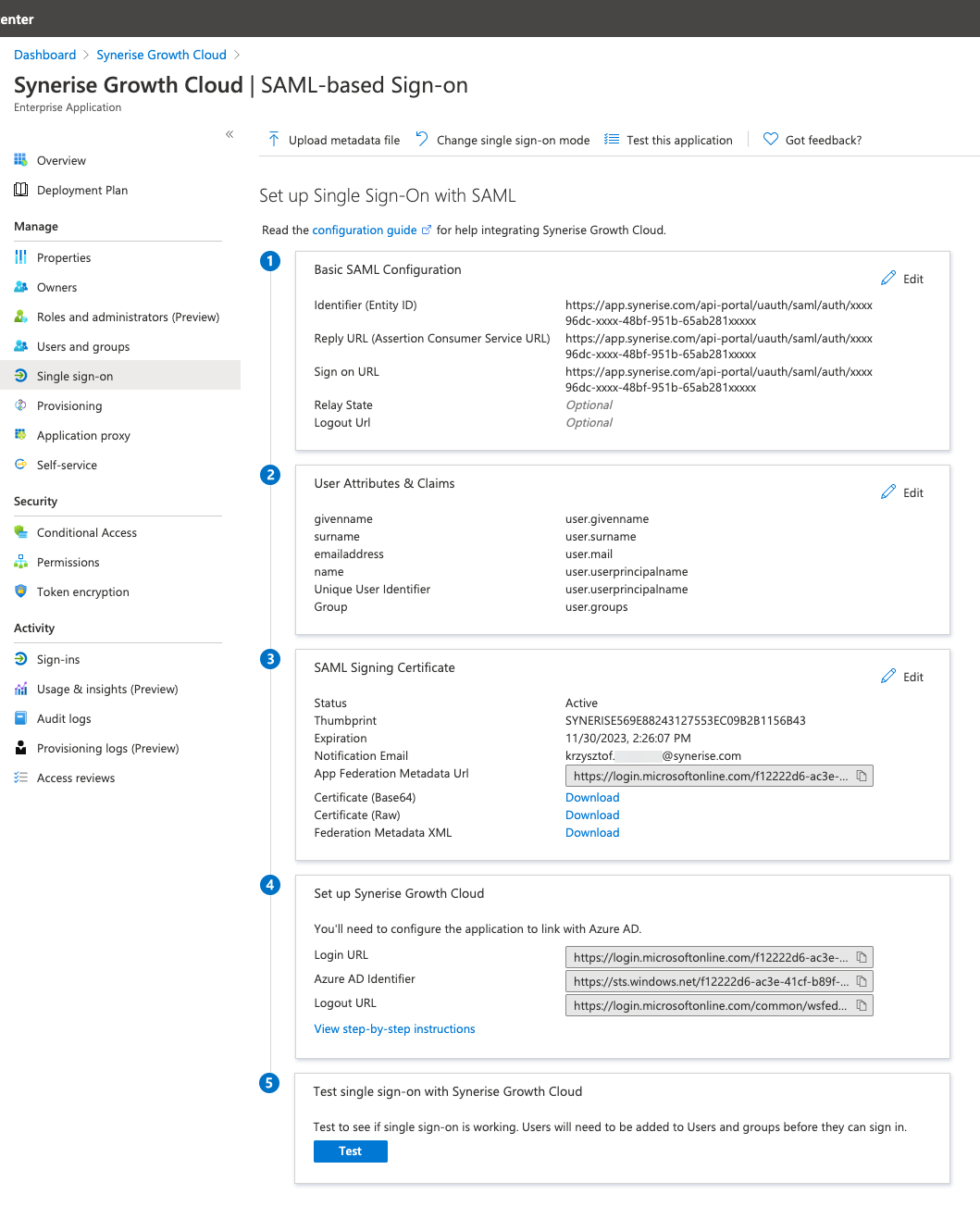
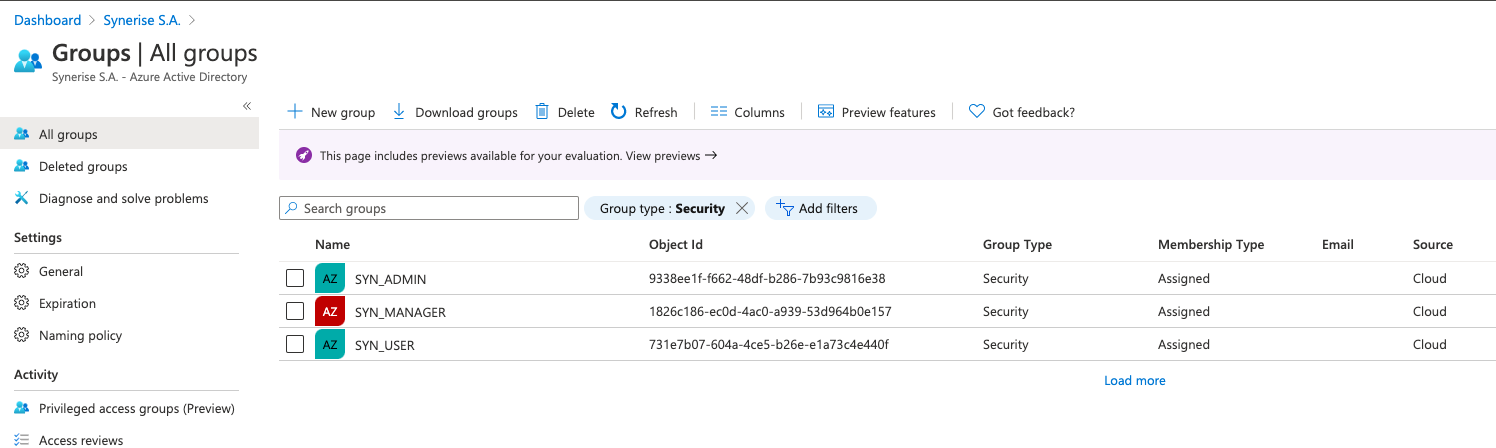
In Microsoft Entra ID portal:
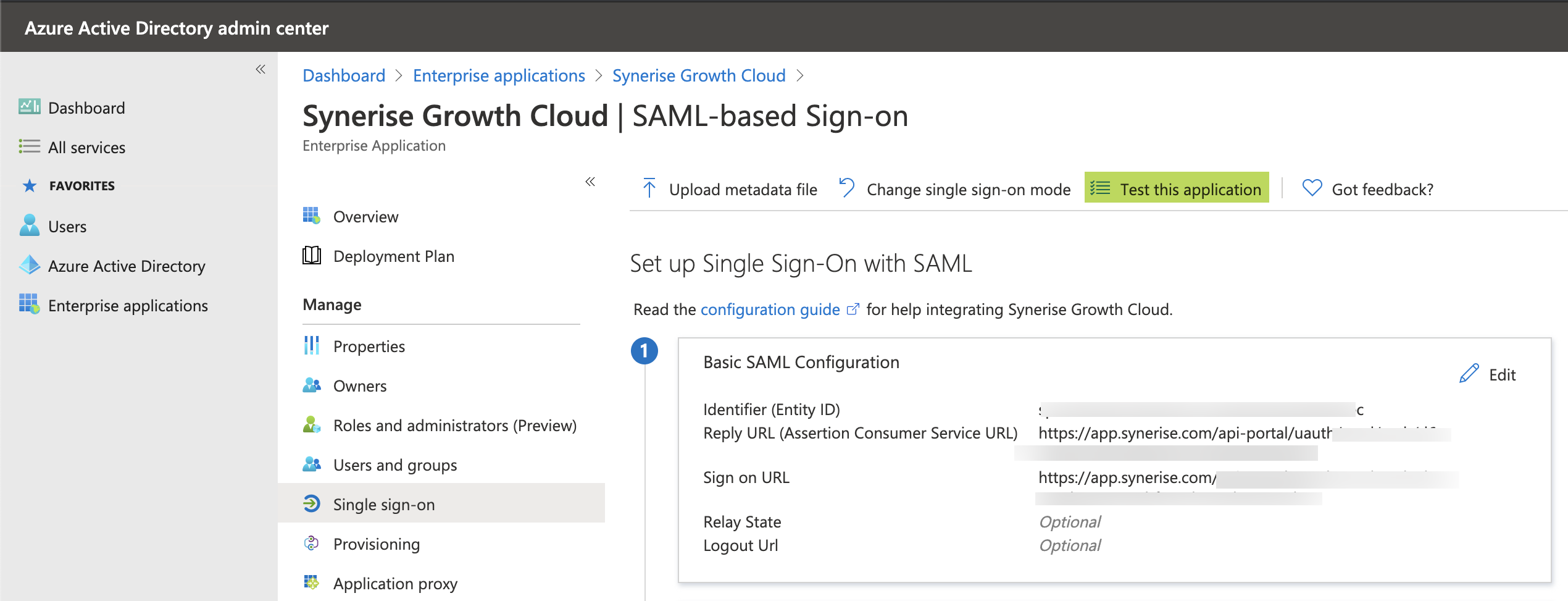
Alternatively, Synerise is available in https://myapplications.microsoft.com/ if you didn't set the Visible to users? option to No in the Enterprise application setup.